SysArmor
Next-Generation Intelligent Endpoint Detection and Forensics System
Hardware-System-Software Co-Design · Comprehensive Audit · Real-time Detection · Semantic Analysis
System Demo
Experience SysArmor in Action

Real-time system monitoring and threat landscape
Dashboard
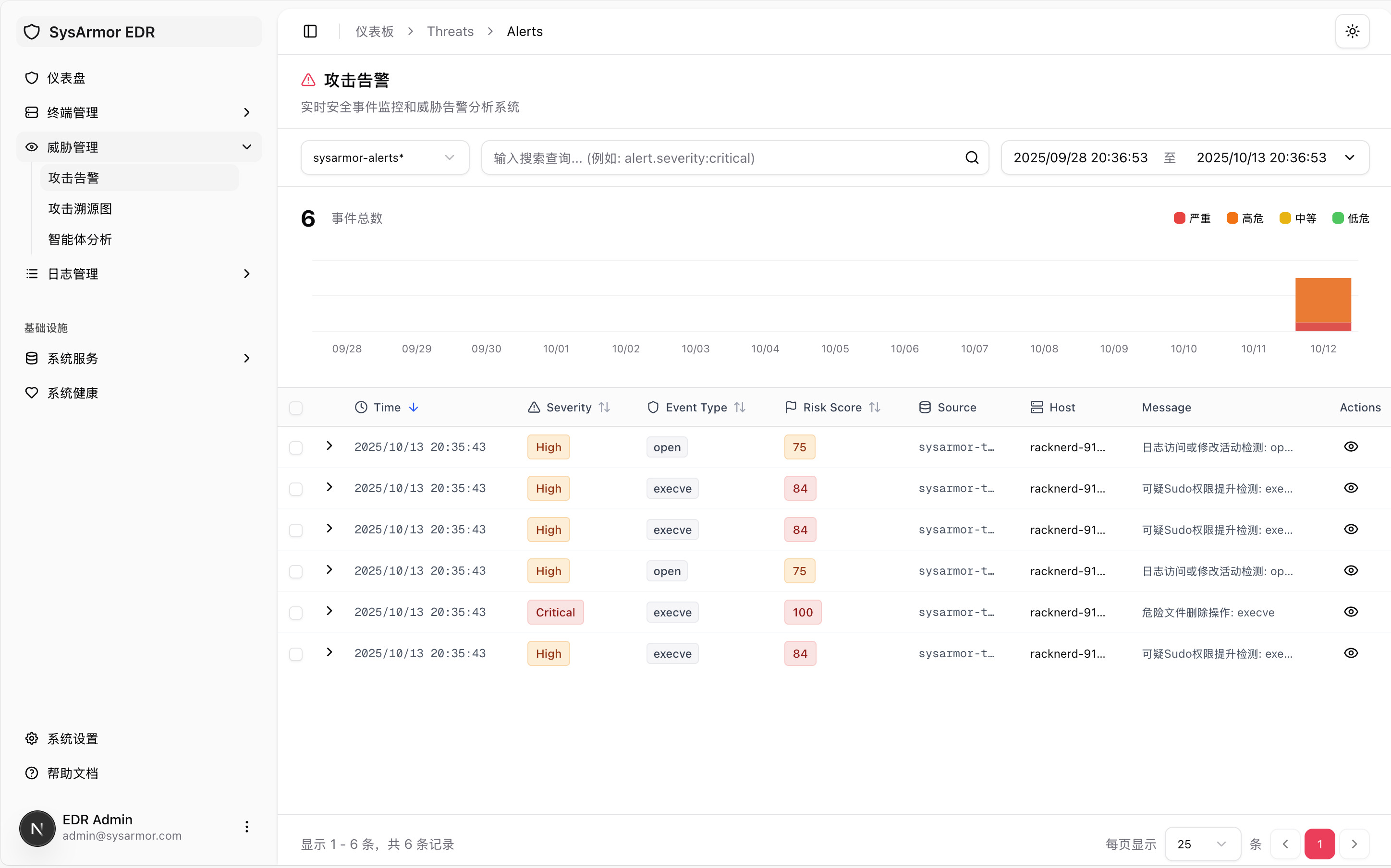
Intelligent detection of anomalies and security events
Threat Alerts

Semantic-level attack behavior understanding
Attack Forensics
System Architecture
Modular Design with End-to-End Data Flow
graph LR
A[Collector] -->|Events| B[Middleware]
B -->|Stream| C[Processor]
C -->|Alerts| D[Indexer]
E[Manager] -.->|Manage| A
E -.->|Manage| B
E -.->|Manage| C
E -.->|Query| D
F[ML Services] -.->|Enhance| C
style A fill:#dbeafe,stroke:#3b82f6,stroke-width:3px
style B fill:#d1fae5,stroke:#10b981,stroke-width:3px
style C fill:#fef3c7,stroke:#f59e0b,stroke-width:3px
style D fill:#fecaca,stroke:#ef4444,stroke-width:3px
style E fill:#e9d5ff,stroke:#9f7aea,stroke-width:3px
style F fill:#fef3c7,stroke:#f59e0b,stroke-width:3px
Platform Infrastructure
Data Middleware
Vector + Kafka for standardized data ingestion
Stream Processing
Flink for real-time event transformation
Index Storage
OpenSearch for alert indexing and retrieval
Control Plane
Manager API for unified orchestration
Web Interface
Alert visualization and operations
Monitoring
Prometheus system monitoring
High Performance
Distributed stream processing for massive data
Modular Design
Loosely coupled architecture for easy extension
Enterprise Ready
Mature open-source components, production-tested
Core Capabilities
Three Major Breakthroughs in Hardware-System-Software Co-Design
Comprehensive Audit
Hardware-System Co-Design
Achieve comprehensive and secure system log collection through hardware offloading and secure resource isolation
Real-time Detection
System-Software Co-Design
Leverage Steiner tree abstraction and threat intelligence knowledge base for accurate threat detection
Enhanced Analysis
Semantic Threat Understanding
Achieve semantic-level threat behavior understanding through attack lifecycle modeling and LLM integration
Roadmap
From Agentless to Agent + ML Solution
Design Principles
Unified Model
Shared data format and interface between Agentless and Agent
Progressive Evolution
Smooth transition from quick deployment to deep collection
Open Extension
Support for open-source components like Wazuh
Future Vision
Build a world-leading intelligent endpoint security platform through continuous innovation in hardware-system-software co-design, providing more powerful and intelligent security protection.
Research Foundation
System Security Research by PKU OS Lab
NoDrop
Secure and trustworthy provenance log collection with multi-threaded architecture
ProvWeb
Malicious website detection from system provenance perspective, F1 Score 93.7%~99.7%
NodLink
First online provenance detection system for efficient real-time APT attack detection
DPUaudit
DPU-assisted near-zero-cost system auditing with pull-based architecture
RT-NoDrop
Predictable and secure system auditing for real-time systems
ProvAudit
Enhancing advanced privacy inference through system provenance data
Query Provenance Analysis
Efficient and robust defense against query-based black-box attacks
KnowHow
Real-time APT attack behavior understanding based on attack lifecycle modeling
Peking University OS Lab
Long-term research on OS security in ubiquitous computing, achieving breakthroughs in system provenance analysis, attack detection and defense, and AI system security.
Learn More